Data Breaches Climbed to a Record High in 2025. How to Protect Your Personal Information
Data Breaches Climbed to a Record High in 2025. How to Protect Your Personal Information
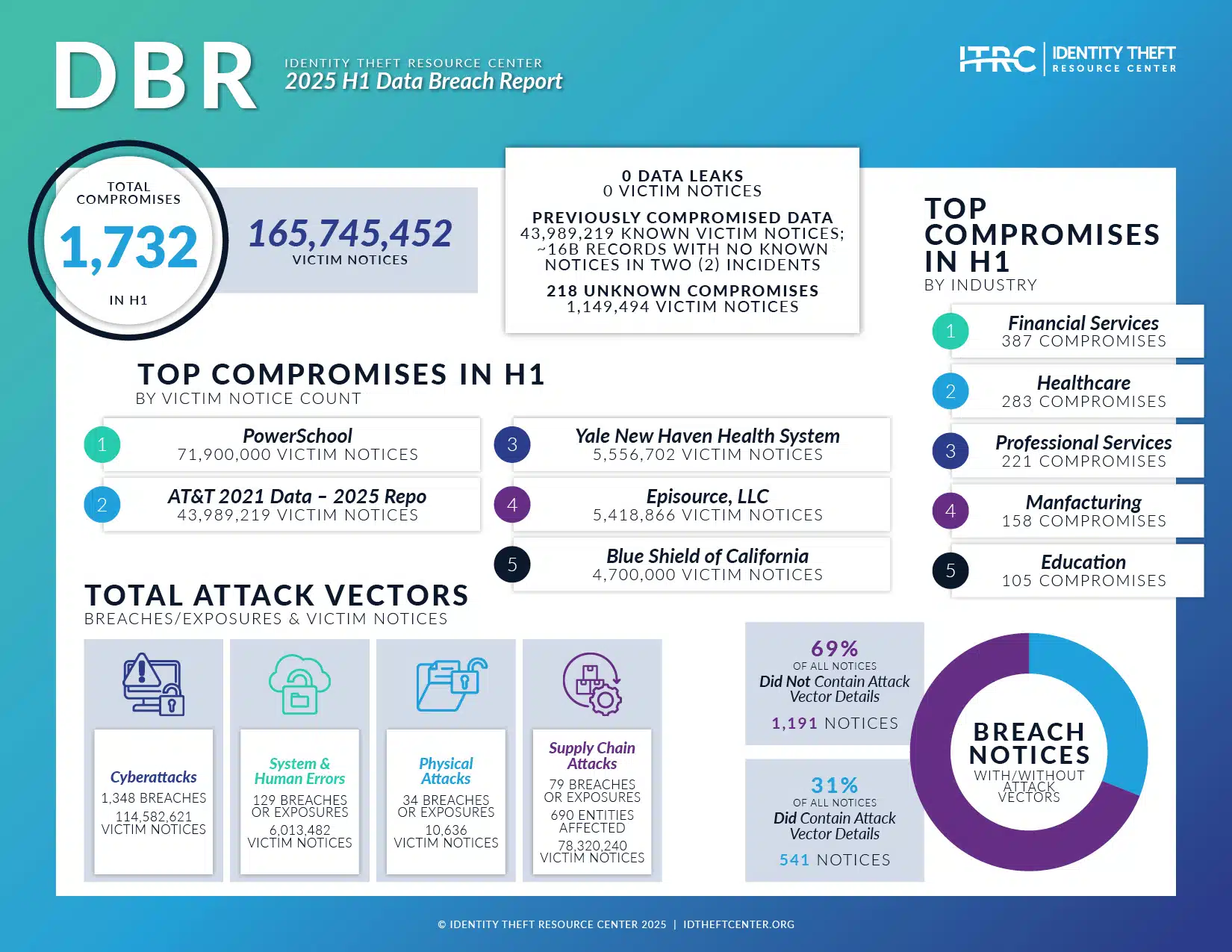
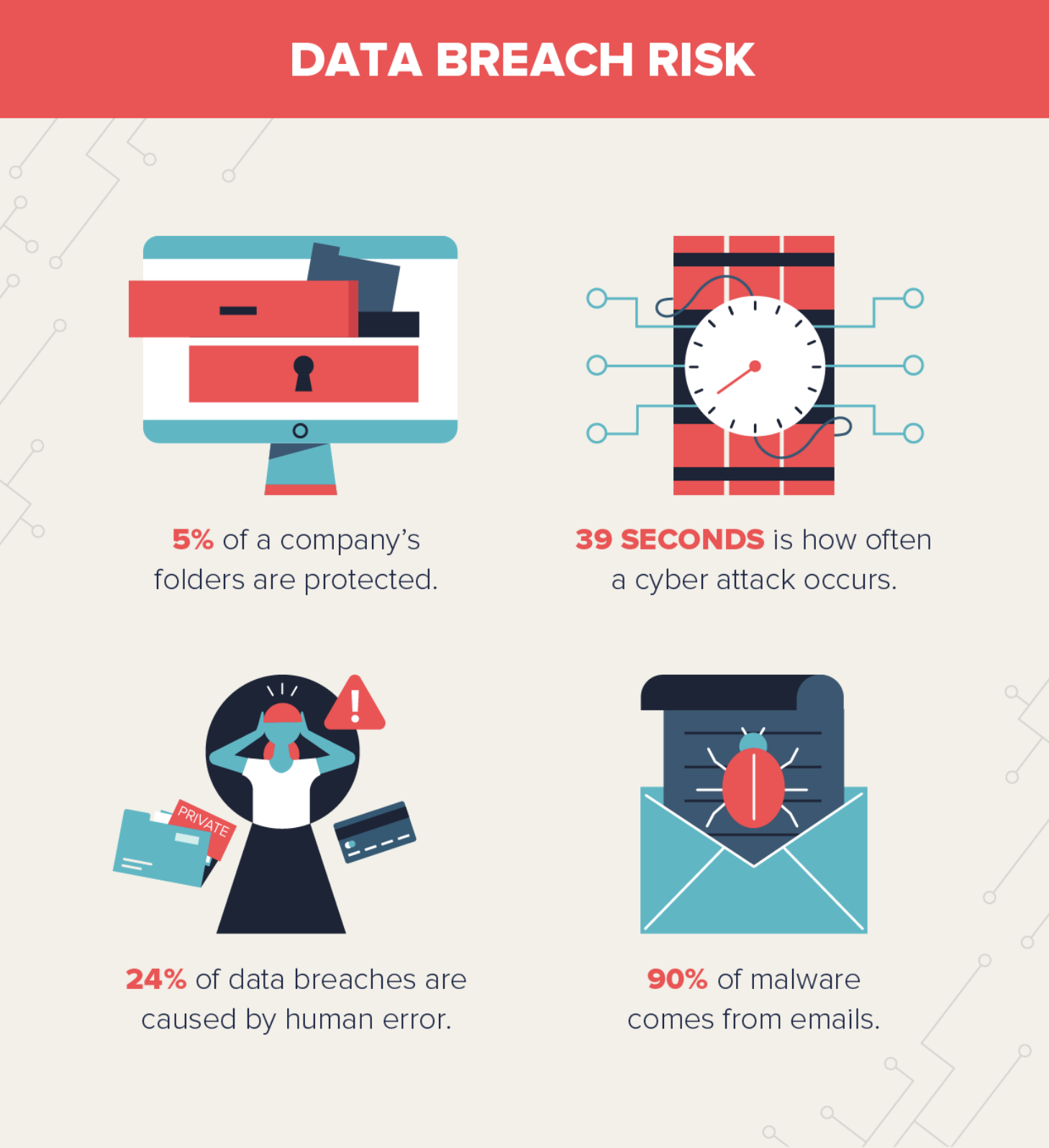
The numbers are staggering. In 2025, reports confirm that the total volume and frequency of data breaches shattered all previous records. Organizations, from massive tech conglomerates to local healthcare providers, fell victim to increasingly sophisticated cyberattacks, leaving millions of consumers exposed to digital fallout and identity theft.
For many of us, the threat feels distant—until it’s personal. I remember the cold dread of receiving an automated email last spring: "We regret to inform you that credentials linked to your old banking profile were found circulating on the dark web." Even though the account was dormant, the realization that my digital identity had been compromised was chilling. This isn't just an abstract headline; it is the new reality of the internet.
The year 2025 has cemented the fact that cyber security is no longer the sole responsibility of IT departments. It is a fundamental life skill. If you hold a social security number, use a cloud service, or connect a smart device to the internet, your personal information is at risk. But the battle is not lost. Understanding the evolving threat landscape is the first critical step toward building robust digital defenses.
We need immediate action and long-term strategy. This comprehensive guide details why the 2025 surge happened and, more importantly, provides the essential steps you must take right now to protect your data and secure your future.
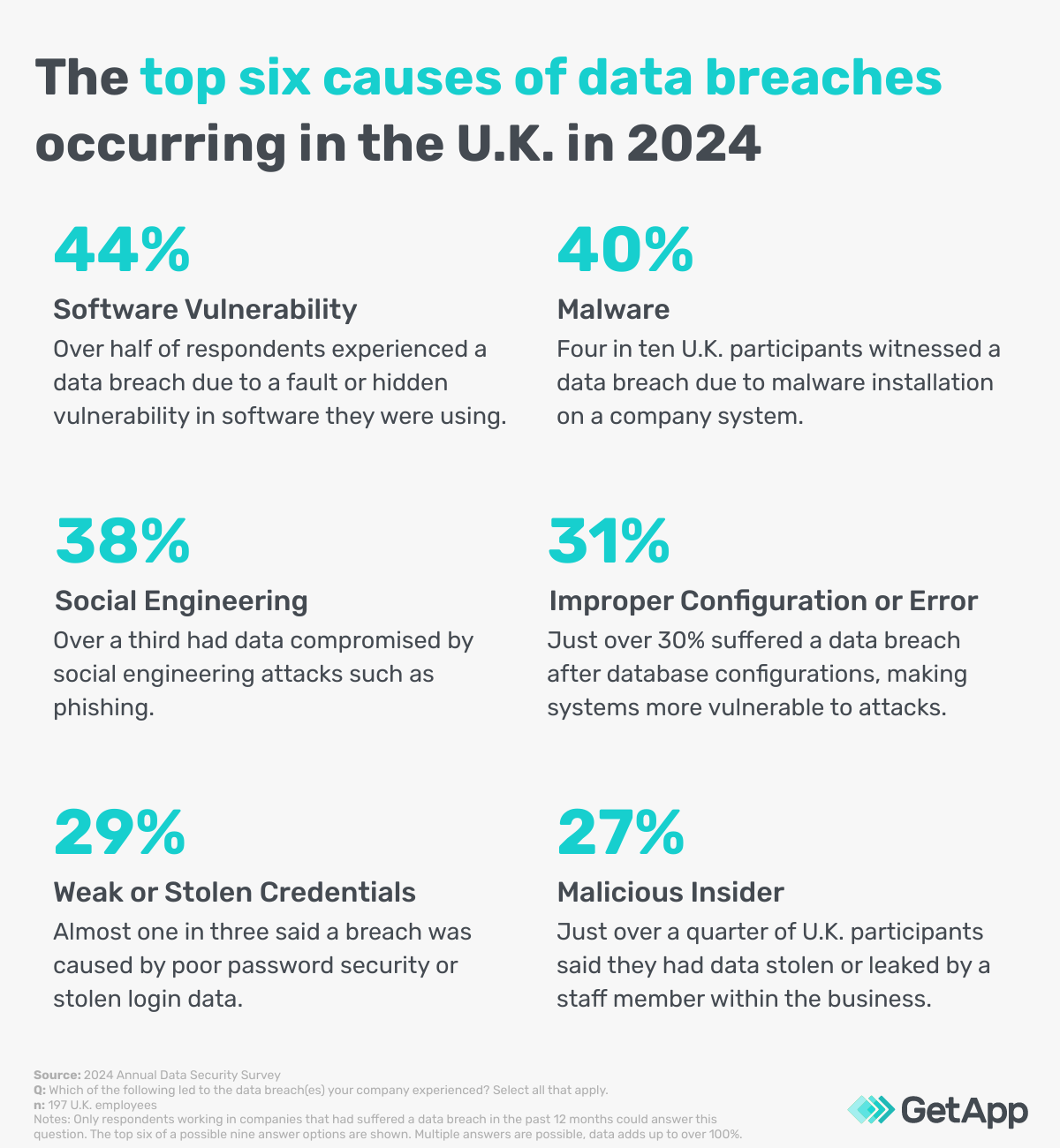
The Anatomy of the 2025 Breach Epidemic: Why the Spike?
The record high breach count didn't happen by accident. It was the convergence of several high-level technological advancements that gave cybercriminals unprecedented scale and speed in their attacks.
The primary driver behind the 2025 crisis was the weaponization of Artificial Intelligence (AI). Attackers utilized sophisticated AI tools to automate everything from generating highly convincing deepfake phishing emails to rapidly identifying zero-day vulnerabilities in corporate networks. Traditional defenses struggled to keep pace with these automated threats.
Furthermore, the persistent challenges related to third-party vendor risk reached a tipping point. Many major breaches in 2025 originated not from the target company itself, but from a smaller, less-secure partner in their supply chain. This supply chain vulnerability created thousands of weak entry points for attackers seeking to compromise sensitive personal data.
Another major factor was the massive increase in interconnected IoT devices. Smart homes, smart offices, and the hyper-connected infrastructure of modern cities provided hackers with an ever-expanding attack surface. Each new connected device often introduced a new potential vulnerability.
The statistics paint a clear picture: the average cost of a data breach rose significantly, and the duration of undetected compromise increased, highlighting the stealth of modern ransomware attacks and digital espionage.
Immediate Defense: Essential Cyber Hygiene Practices You Must Adopt Now
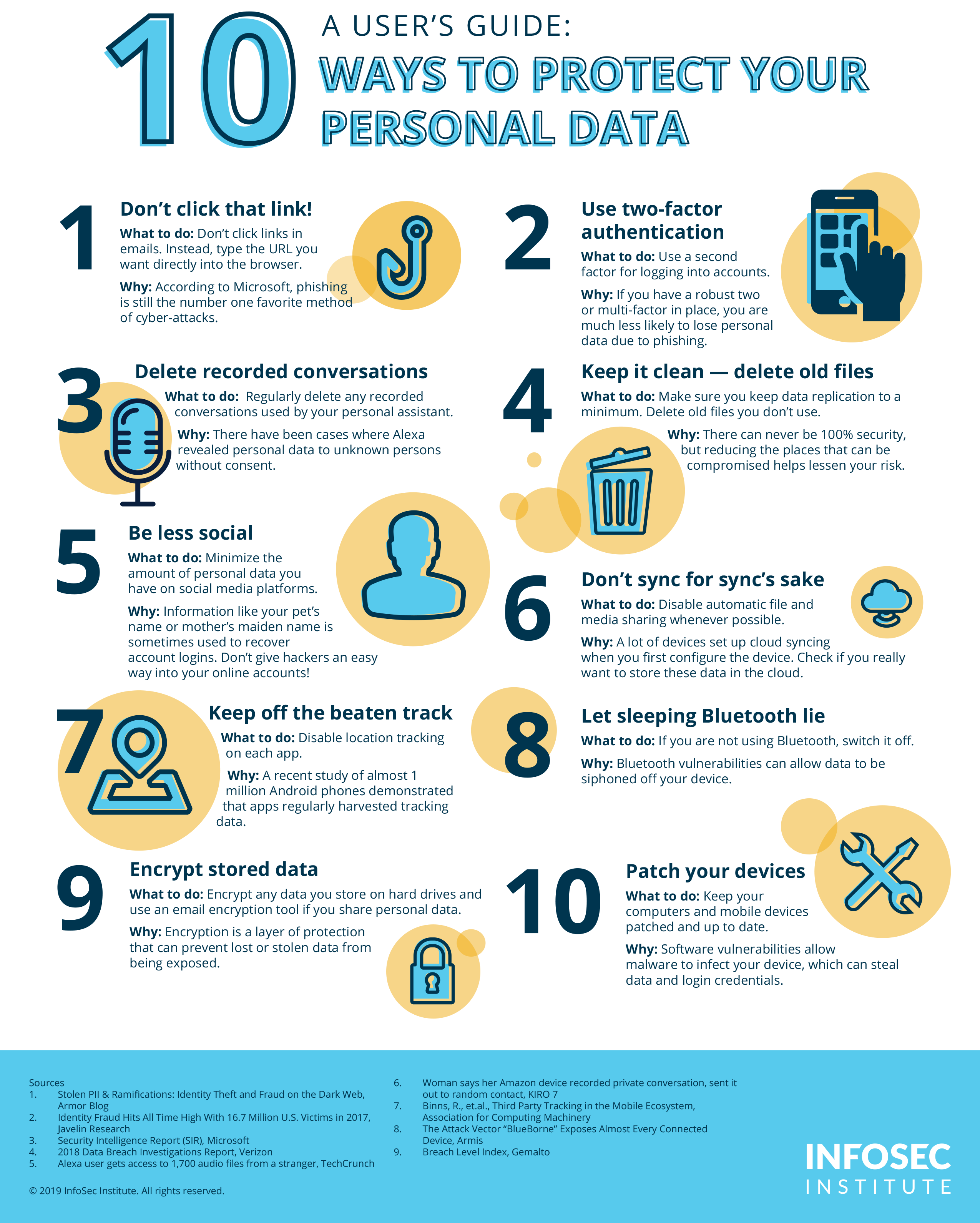
While global entities grapple with systemic infrastructure defense, individuals must focus on strengthening their own immediate digital perimeter. These actions are non-negotiable for anyone using the internet today.
1. Implement Multi-Factor Authentication (MFA) Everywhere
If you take only one piece of advice from this article, let it be this: Enable Multi-Factor Authentication (also known as Two-Factor Authentication or 2FA) on every single account that offers it. MFA is the single most effective barrier against account takeover attacks, rendering stolen passwords useless without the secondary physical device (like your phone).
- Prioritize email, banking, social media, and financial investment platforms.
- Use authenticator apps (like Google Authenticator or Authy) over SMS codes, as SMS can be hijacked via SIM-swapping schemes.
2. Abandon Weak and Reused Passwords
Password reuse is the digital equivalent of leaving the keys to your house, car, and office hanging on the same hook. If one service is breached, every account sharing that password is immediately compromised.
- Utilize a dedicated, encrypted password manager (e.g., 1Password, LastPass, Bitwarden) to generate and store unique, complex passwords for all services.
- Aim for passwords that are at least 16 characters long, mixing symbols, numbers, and cases.
3. Stay Vigilant Against Phishing Scams
Phishing remains the primary method for gathering credentials. In 2025, AI-powered phishing emails are nearly indistinguishable from legitimate communications. They utilize perfect grammar and reference personal details scraped from public records.
- Always check the sender’s actual email address, not just the display name.
- Hover your mouse over any links before clicking to check the destination URL. If it looks suspicious or misspelled, do not click.
- Be skeptical of urgent requests for personal data, particularly those related to banking or package delivery.
4. Update Your Software Promptly
Software updates aren't just for new features; they are crucial security patches designed to close vulnerabilities that hackers are actively exploiting. Delayed updates leave you exposed.
- Enable automatic updates for your operating system (Windows, macOS), web browser, and mobile apps.
- Don't ignore update prompts for routers and smart home devices.
Beyond the Basics: Advanced Tactics for Digital Identity Protection
For those serious about mitigating the risks highlighted by the 2025 breach record, a more strategic, proactive defense posture is required. This involves minimizing your digital footprint and actively monitoring for signs of compromise.
Proactive Monitoring and Data Minimization
You cannot secure what you don't know you have. Take inventory of your digital identity. Start practicing "data minimalism"—only share and store the data absolutely necessary.
One powerful tool is identity monitoring. Services that actively scan the dark web for your email addresses, phone numbers, and credit card numbers can provide early warning, allowing you to change passwords before criminals can use the stolen data.
- Credit Freezes: Place a freeze on your credit reports with all three major bureaus (Equifax, Experian, TransUnion). This prevents identity thieves from opening new lines of credit in your name, as the credit check cannot be completed. This is perhaps the most effective protective measure against financial identity theft.
- Review Permissions: Regularly audit the permissions you have granted to third-party applications on your social media and cloud services (Google Drive, Dropbox). Revoke access for any apps you no longer use.
- Use Separate Emails: Maintain one primary email for sensitive financial and communication purposes and a secondary "burner" email for newsletters, online shopping, and forum sign-ups. If the secondary email is breached, the risk to your critical accounts is lower.
Responding to a Breach: The Recovery Mindset
The truth is, even with perfect security hygiene, large corporate breaches are outside of your control. Therefore, knowing how to respond rapidly is crucial to minimizing damage.
If you receive notification that your data has been compromised in a major corporate breach, assume the worst and act immediately:
Step 1: Change Passwords. Even if you only think the affected account's password was exposed, change the password on that account and any other accounts that shared the same credential.
Step 2: Review Financial Statements. Closely examine credit card statements, bank accounts, and investment portfolios for unauthorized transactions. Report anything suspicious immediately to your financial institution.
Step 3: Check Your Credit Report. Order a free credit report from AnnualCreditReport.com. Look for unfamiliar accounts or inquiries that signal attempted identity theft.
Step 4: Report the Incident. File a report with the Federal Trade Commission (FTC) if identity theft is confirmed. This step generates a recovery plan and an official ID Theft Affidavit that can be used when disputing fraudulent charges or accounts.
Securing Your Future Digital Life
The record data breaches of 2025 serve as a stark reminder that the digital landscape is fraught with peril. However, panic is not a defense strategy. Education, vigilance, and the deployment of strong cyber hygiene practices are the necessary tools for navigating this new era.
Protecting your personal information is an ongoing process, not a one-time setup. By implementing MFA, using robust password management, and proactively minimizing your digital footprint, you can dramatically shift the risk balance in your favor. Take control of your digital identity today; the cost of inaction is too high to bear.
Data breaches climbed to a record high in 2025. How to protect your personal information
Data breaches climbed to a record high in 2025. How to protect your personal information Wallpapers
Collection of data breaches climbed to a record high in 2025. how to protect your personal information wallpapers for your desktop and mobile devices.
Vibrant Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Artwork for Desktop
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.

Stunning Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Capture for Desktop
A captivating data breaches climbed to a record high in 2025. how to protect your personal information scene that brings tranquility and beauty to any device.
Dynamic Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Capture Photography
This gorgeous data breaches climbed to a record high in 2025. how to protect your personal information photo offers a breathtaking view, making it a perfect choice for your next wallpaper.

Artistic Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Capture in 4K
Find inspiration with this unique data breaches climbed to a record high in 2025. how to protect your personal information illustration, crafted to provide a fresh look for your background.
Spectacular Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information View in 4K
This gorgeous data breaches climbed to a record high in 2025. how to protect your personal information photo offers a breathtaking view, making it a perfect choice for your next wallpaper.
Gorgeous Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Wallpaper in HD
This gorgeous data breaches climbed to a record high in 2025. how to protect your personal information photo offers a breathtaking view, making it a perfect choice for your next wallpaper.

Mesmerizing Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Capture Art
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.

Detailed Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Photo Collection
Explore this high-quality data breaches climbed to a record high in 2025. how to protect your personal information image, perfect for enhancing your desktop or mobile wallpaper.
Spectacular Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Capture Collection
Immerse yourself in the stunning details of this beautiful data breaches climbed to a record high in 2025. how to protect your personal information wallpaper, designed for a captivating visual experience.

Breathtaking Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Artwork Illustration
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.

Mesmerizing Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Scene Collection
Discover an amazing data breaches climbed to a record high in 2025. how to protect your personal information background image, ideal for personalizing your devices with vibrant colors and intricate designs.

Gorgeous Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Moment for Desktop
This gorgeous data breaches climbed to a record high in 2025. how to protect your personal information photo offers a breathtaking view, making it a perfect choice for your next wallpaper.
Mesmerizing Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Design Nature
Transform your screen with this vivid data breaches climbed to a record high in 2025. how to protect your personal information artwork, a true masterpiece of digital design.

Spectacular Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information View Photography
A captivating data breaches climbed to a record high in 2025. how to protect your personal information scene that brings tranquility and beauty to any device.
Vivid Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Moment Illustration
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.

Breathtaking Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Design Photography
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.

Gorgeous Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Picture Nature
A captivating data breaches climbed to a record high in 2025. how to protect your personal information scene that brings tranquility and beauty to any device.

Vivid Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Moment Illustration
Transform your screen with this vivid data breaches climbed to a record high in 2025. how to protect your personal information artwork, a true masterpiece of digital design.

Beautiful Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Design Digital Art
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.

Breathtaking Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Artwork for Your Screen
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.
Download these data breaches climbed to a record high in 2025. how to protect your personal information wallpapers for free and use them on your desktop or mobile devices.